Roles and Responsibilities of Cyber Security Professionals

The cybersecurity industry is currently flooding with jobs. It has been reported that fewer people are required to fill all the cybersecurity roles. The leading roles organizations are advertising for are covered in the sections.
Penetration testers and vulnerability testers
The primary role of protecting the organization from malicious hackers is to check the network or system vulnerability-free and fix it before the hacker finds the hole.
Pen testers, also known as white hackers, try to compromise the system or network as requested by the owners of these systems. Due to this, the demand for pen testers increases exponentially in the job market.
In every organization, security measures might be implemented to secure the organization. Still, it is essential to strengthen it by utilizing various security tools because people are looking to breach them.
Using typical hacking or reconnaissance tools like Metasploit or Wireshark, penetration testers examine the organization's security posture. It will also involve checking the source code for the systems organizations develop to support their operations.
Cybersecurity consultants
Organization worldwide focuses on improving security measure and intend to reduce their financial burden. Due to this, many top companies hire full-time employees to analyze the organization's security.
In contrast to other IT activities like helpdesk support, some cybersecurity roles could be more routine and can thus be performed occasionally or twice a month.
Cybersecurity consultants are highly skilled professionals who protect computer systems, networks, and digital infrastructure from potential security threats and vulnerabilities. Their primary role is to assess an organization's security measures, identify weaknesses, and develop strategies to mitigate risks. These consultants conduct thorough security audits, risk assessments, and vulnerability testing to ensure that organizations comply with industry standards and best practices. They also play a crucial role in incident response, helping organizations recover from security breaches and providing guidance on improving security protocols.
Cybersecurity managers
The primary role of cybersecurity managers is to ensure the protection and security of an organization's digital assets and information systems. They are responsible for developing and implementing effective cybersecurity strategies, policies, and procedures to safeguard against potential threats and attacks. Cybersecurity managers oversee the day-to-day operations of the organization's security measures, including monitoring networks and systems for any vulnerabilities or breaches, conducting risk assessments, and implementing appropriate controls.
Cybersecurity analysts
Cybersecurity analysts' primary role is to secure an organization's digital assets and sensitive information from cyber threats and attacks. This is accomplished by continuously monitoring networks and systems for suspicious activity, discovering vulnerabilities, and responding to security issues. Cybersecurity analysts evaluate the organization's security procedures, make recommendations for changes, and put security policies and technologies in place to prevent intrusions. Their constant monitoring and proactive activities are critical in reducing risks, guaranteeing data confidentiality, integrity, and availability, and protecting the firm from cyber-attacks.
Cybersecurity engineers:
Cybersecurity engineers protect computer systems, networks, and data from illegal access, breaches, and cyber threats. Their primary task is to identify potential vulnerabilities and develop risk mitigation methods. They design and implement security mechanisms, including firewalls, encryption protocols, and intrusion detection systems, to secure sensitive information and ensure the integrity of digital infrastructure. Cybersecurity engineers also monitor and analyze network traffic, audit security, and respond to events immediately. They stay current on the newest security trends and technology, continually reviewing and improving the organization's security posture.
Chief Information Security Officers (CISOs)
Chief Information Security Officers (CISOs) safeguard an organization's information assets and ensure a secure digital environment. CISOs are in charge of creating and enforcing comprehensive information security plans and procedures. They are responsible for designing and implementing security measures to protect the organization's systems, networks, and data from potential dangers, including cyberattacks and data breaches. CISOs are also responsible for identifying and managing risks, conducting regular security audits, and ensuring compliance with applicable rules and industry standards.
Chief Security Officers (CSOs)
CSOs are responsible for the overall security and protection of an organization's assets, which include physical property, data, and persons. They are responsible for creating and implementing comprehensive security plans, policies, and processes that protect the firm from potential threats and dangers. CSOs also monitor and keep updated on evolving security trends and legislation. Compliance must ensure the business remains proactive and adaptable in dealing with possible security threats. Finally, the CSO is crucial in safeguarding the organization's reputation, ensuring business continuity, and providing a safe environment for all stakeholders.
Computer system administrators:
Computer system administrators are responsible for managing and maintaining an organization's computer systems and networks. Their primary responsibility is to ensure that the systems operate efficiently and securely. This includes installing and configuring software and hardware, monitoring system performance, troubleshooting issues, and performing regular backups. They are also responsible for managing user accounts, granting permissions, and ensuring data integrity and security. Additionally, computer system administrators play a crucial role in implementing and enforcing IT policies and procedures and keeping up with the latest technological advancements to ensure the organization's systems are up-to-date and secure.
Now, we shall discuss top companies and industries that hire these skilled professionals. Moreover, we shall discuss the average pay scale of cybersecurity professionals.
Companies hire cybersecurity specialists:
- IBM Security
- Deloitte
- Amazon
- FireEye
- Cisco
- Microsoft
Industries hire cybersecurity specialists:
- IT security firms and consulting companies
- Financial institutions
- Healthcare organizations
- Retail and e-commerce companies
- Energy and utility companies
- Education institutions
Average pay scale of Cybersecurity specialist:
The average pay scale of cybersecurity specialists can vary significantly based on factors such as experience, location, education, and the specific role within the field.
Entry-level penetration testers and vulnerability testers can expect an annual salary ranging from $60,000 to $90,000. These individuals often have limited experience but may hold relevant certifications like Certified Ethical Hacker (CEH) or CompTIA Security+.
In conclusion, the roles and responsibilities of cybersecurity professionals are critical in protecting organizations' information assets and maintaining a secure digital environment. Cybersecurity professionals are responsible for identifying potential threats and vulnerabilities, developing and implementing security strategies and policies, conducting regular security audits, and ensuring compliance with relevant regulations and industry standards. They also play a vital role in promoting security awareness and cybersecurity training programs to educate employees about best practices for information security.
Find a course provider to learn Cyber Security
Java training | J2EE training | J2EE Jboss training | Apache JMeter trainingTake the next step towards your professional goals in Cyber Security
Don't hesitate to talk with our course advisor right now
Receive a call
Contact NowMake a call
+1-732-338-7323Take our FREE Skill Assessment Test to discover your strengths and earn a certificate upon completion.
Enroll for the next batch
Cyber Security Online Training
- Dec 15 2025
- Online
Cyber Security
- Dec 16 2025
- Online
Cyber Security Online Training
- Dec 17 2025
- Online
Cyber Security
- Dec 18 2025
- Online
Cyber Security Online Training
- Dec 19 2025
- Online
Related blogs on Cyber Security to learn more

How Security Classification Guides Strengthen Data Protection in Modern Cybersecurity
A Security Classification Guide (SCG) defines data protection standards, ensuring sensitive information is handled securely across all levels. By outlining confidentiality, access controls, and declassification procedures, SCGs strengthen cybersecuri
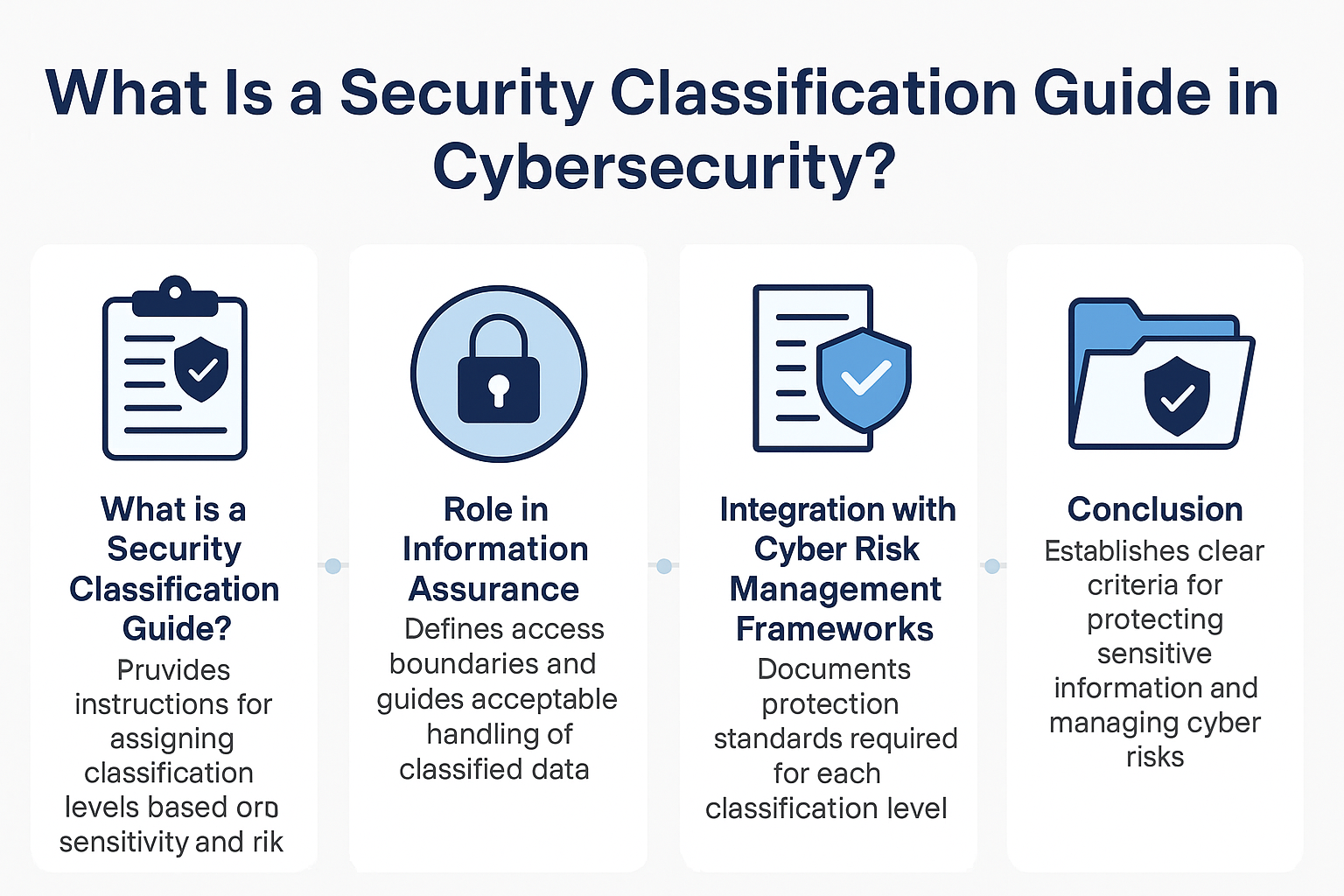
What Is a Security Classification Guide in Cybersecurity?
A Security Classification Guide (SCG) defines how to categorize information assets by sensitivity, with clear instructions from authorized officials to ensure consistent, compliant data handling.

Cybersecurity Training: Powering Digital Defense
Explore top cybersecurity training programs in the USA to meet rising demand in digital defense. Learn about certifications, salaries, and career opportunities in this high-growth field.

What Does a Cybersecurity Analyst Do? 2025
Discover the vital role of a Cybersecurity Analyst in 2025, protecting organizations from evolving cyber threats through monitoring, threat assessment, and incident response. Learn about career paths, key skills, certifications, and why now is the be
What essential skills and trends should cybersecurity professionals navigate in 2024?
Cybersecurity professionals in 2024 must master a diverse skillset, from cloud security and AI to soft skills like communication and problem-solving, to stay ahead of evolving cyber threats and regulations.

What Does a Cybersecurity Analyst Do?
Learn about the role of a Cybersecurity Analyst, responsible for protecting an organization's computer networks from cyberattacks.

10 Popular Cybersecurity Certifications
From CompTIA Security+ to CISSP, these certifications can boost your career and demonstrate your commitment to protecting computer systems and networks.

What are the most popular technical certifications for future career advancement?
Unlock your potential with insights into 5 popular technical certifications for future career growth, spanning cybersecurity, blockchain, cloud computing and more. Explore pathways for professional advancement today.

How to Become a Security Architect: 2024 Career Guide
How to Become a Security Architect: 2024 Career Guide In today's fast-paced and digitally interconnected world, the role of a Security Architect
Latest blogs on technology to explore
From Student to AI Pro: What Does Prompt Engineering Entail and How Do You Start?
Explore the growing field of prompt engineering, a vital skill for AI enthusiasts. Learn how to craft optimized prompts for tools like ChatGPT and Gemini, and discover the career opportunities and skills needed to succeed in this fast-evolving indust

How Security Classification Guides Strengthen Data Protection in Modern Cybersecurity
A Security Classification Guide (SCG) defines data protection standards, ensuring sensitive information is handled securely across all levels. By outlining confidentiality, access controls, and declassification procedures, SCGs strengthen cybersecuri

Artificial Intelligence – A Growing Field of Study for Modern Learners
Artificial Intelligence is becoming a top study choice due to high job demand and future scope. This blog explains key subjects, career opportunities, and a simple AI study roadmap to help beginners start learning and build a strong career in the AI

Java in 2026: Why This ‘Old’ Language Is Still Your Golden Ticket to a Tech Career (And Where to Learn It!
Think Java is old news? Think again! 90% of Fortune 500 companies (yes, including Google, Amazon, and Netflix) run on Java (Oracle, 2025). From Android apps to banking systems, Java is the backbone of tech—and Sulekha IT Services is your fast track t
From Student to AI Pro: What Does Prompt Engineering Entail and How Do You Start?
Learn what prompt engineering is, why it matters, and how students and professionals can start mastering AI tools like ChatGPT, Gemini, and Copilot.

Cyber Security in 2025: The Golden Ticket to a Future-Proof Career
Cyber security jobs are growing 35% faster than any other tech field (U.S. Bureau of Labor Statistics, 2024)—and the average salary is $100,000+ per year! In a world where data breaches cost businesses $4.45 million on average (IBM, 2024), cyber secu

SAP SD in 2025: Your Ticket to a High-Flying IT Career
In the fast-paced world of IT and enterprise software, SAP SD (Sales and Distribution) is the secret sauce that keeps businesses running smoothly. Whether it’s managing customer orders, pricing, shipping, or billing, SAP SD is the backbone of sales o

SAP FICO in 2025: Salary, Jobs & How to Get Certified
AP FICO professionals earn $90,000–$130,000/year in the USA and Canada—and demand is skyrocketing! If you’re eyeing a future-proof IT career, SAP FICO (Financial Accounting & Controlling) is your golden ticket. But where do you start? Sulekha IT Serv

Train Like an AI Engineer: The Smartest Career Move You’ll Make This Year!
Why AI Engineering Is the Hottest Skillset Right Now From self-driving cars to chatbots that sound eerily human, Artificial Intelligence is no longer science fiction — it’s the backbone of modern tech. And guess what? Companies across the USA and Can
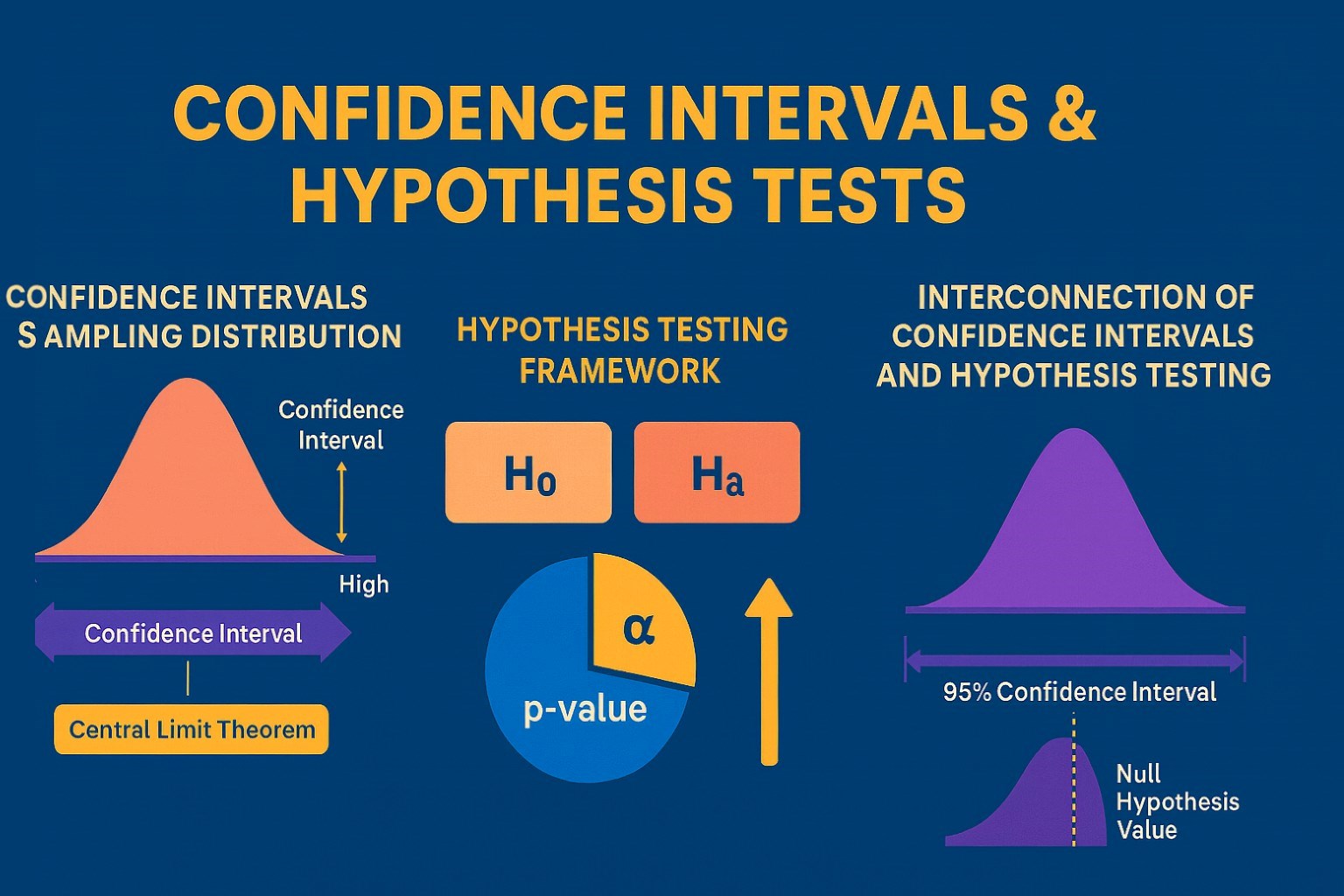
Confidence Intervals & Hypothesis Tests: The Data Science Path to Generalization
Learn how confidence intervals and hypothesis tests turn sample data into reliable population insights in data science. Understand CLT, p-values, and significance to generalize results, quantify uncertainty, and make evidence-based decisions.
