How To Select The Best Vulnerability Management Tools?
There is a wide array of vulnerability management tools in the market to aid the security professionals with the detection and fixing of issues of vulnerability in the system. There are various quality vulnerable management products and only those vulnerable management tools should be chosen that apply to the environment of an organization. While selecting the tools it should always be remembered that there is no replacement for hands-on-experience with a product.
Another important criterion while choosing the tools is the user experience with the tool. This is of importance if the access needs to be extended beyond the use of the security personnel to the systems engineers, who may not be well versed in employing the services of such products. All the employees of an organization should be comfortable in using these security tools, otherwise the utility of such tools become useless.
There are many other factors which need to be considered while choosing such vulnerability management tools. Hence, it can be seen that detecting the vulnerabilities in a security system of an organization is of utmost importance and for such purpose companies hire vulnerable management analysts and you get a high profile job like this by doing a vulnerable management training course.
Some important features of such tools that should be considered while evaluating a solution are stated below.
Factors That Need To Be Considered While Selecting Vulnerability Management Tools Are:
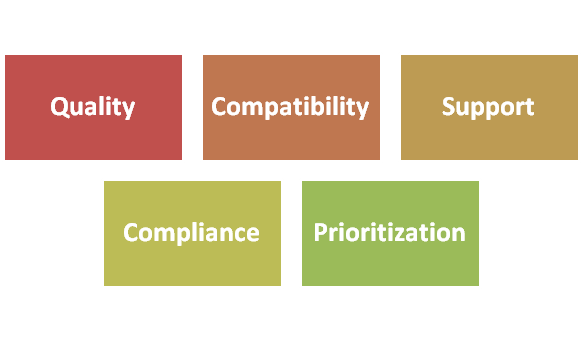
Quality and Speed of Updates:
The frequency at which the vendor releases vulnerability updates should be taken into consideration. One way to help in the vulnerability assessment process is to choose high profile vulnerability and determine the gap between the time the vulnerability was declared and the vendor released the update.
Compatibility with Your Environment:
It should be determined whether the product released by the vendor includes the coverage of the infrastructure components, major applications and operating systems in the environment.
Support for Cloud Services:
It should be ascertained that product has the ability to detect flaws with configurations in the environment of any tools being employed for the platform as a service, infrastructure as a service and software as a service.
Compliance:
It should be noted whether the product offers support for compliance programs that are applicable to the environment of an organization. If there is a problem with the PCI DSS, it should be ascertained whether the vulnerable management product could be used to carry out the scans and complete the self-assessments. Thus, for the growing importance of vulnerability management analyst in organizations, boost your career by learning vulnerable management analysis.
Prioritization:
It should be ascertained what information factors are present in the product’s prioritization algorithm. It should be determined whether the product includes a blend of automated prioritization or any manual configuration that permits an organization to achieve its goals effectively.
Active and Passive Detection:
This is also another important factor to be considered while choosing vulnerability management tools. It should be noted whether the product integrates passive vulnerability detection, which is based on the observation of network traffic and the traditional active system scanning.
Authenticated and Unauthenticated Scanning.:
It should be ascertained whether the tool permits the installation of agent on the system of an organization to carry out validated scans that minimize false positive rates and whether an agent is available for the major platforms.
Remediation Guidance:
It should be ascertained as to what kind of remediation solution the tool offers for the detected vulnerabilities. It should be found out from the product’s reports whether adequate information is provided to repair the vulnerability or whether more additional research needs to be carried out.
Vendor Support:
It should be determined while choosing vulnerable management tool, what kind of support choices are available to an organization as part of the contract and the assured response time of the vendor should be taken into consideration.
Use this feature list as a starting point for your own selection process. You’ll want to develop your own prioritized list of criteria and use it to rank potential products for use in your organization.
Get a high caliber job in a reputed organization by doing a vulnerability management certification course.
Take the next step towards your professional goals in Vulnerability Management
Don't hesitate to talk with our course advisor right now
Receive a call
Contact NowMake a call
+1-732-338-7323Related blogs on Vulnerability Management to learn more

Why Vulnerability Is A Mandatory Process For All Organizations?
Vulnerability management is the repetitive practice of classifying, mitigating, identifying and remediating vulnerabilities, especially in the firmware and softwares. Vulnerability management is an inherent part of network and computer security. Vuln

Exploring the Process Of Vulnerability Management
Vulnerability management is the cyclical practice of classifying, mitigating, identifying and remediating vulnerabilities, especially in the firm wares. Some unknown vulnerabilities, such as zero day attack, is detected with fuzz testing. This method

A Shift from Manual To Automated Vulnerability Management With SCAP
The Security Content Automation Protocol (SCAP) is a technique for employing specific standards to help in automated vulnerability management, policy compliance evaluation (e.g., FISMA compliance) and measurement. The National Vulnerability Database

Advanced Vulnerability Management Tool Features That Sets Them Apart
Vulnerability management tools have the capability of identifying and detecting assets in IT. They identify vulnerabilities and offer the descriptions of the vulnerabilities, as well as the links to various forms of rectification and develop a multit

Advanced Vulnerability Management Tool Features That Sets TAdvanced Vulnerability Management Tool Features That Sets Them Aparth
Vulnerability management tools have the capability of identifying and detecting assets in IT. They identify vulnerabilities and offer the descriptions of the vulnerabilities, as well as the links to various forms of rectification and develop a multit
Latest blogs on technology to explore

Drug Safety & Pharmacovigilance: Your 2026 Career Passport to a Booming Healthcare Industry!
Why This Course Is the Hottest Ticket for Science Grads & Healthcare Pros (No Lab Coat Required!)" The Exploding Demand for Drug Safety Experts "Did you know? The global pharmacovigilance market is set to hit $12.5B by 2026 (Grand View Research, 202

Launch Your Tech Career: Why Mastering AWS Foundation is Your Golden Ticket in 2026
There’s one skill that can open all those doors — Amazon Web Services (AWS) Foundation
Data Science in 2026: The Hottest Skill of the Decade (And How Sulekha IT Services Helps You Master It!)
Data Science: The Career that’s everywhere—and Nowhere Near Slowing Down "From Netflix recommendations to self-driving cars, data science is the secret sauce behind the tech you use every day. And here’s the kicker: The U.S. alone will have 11.5 mill

Salesforce Admin in 2026: The Career Goldmine You Didn’t Know You Needed (And How to Break In!)
The Salesforce Boom: Why Admins Are in Crazy Demand "Did you know? Salesforce is the 1 CRM platform worldwide, used by 150,000+ companies—including giants like Amazon, Coca-Cola, and Spotify (Salesforce, 2025). And here’s the kicker: Every single one

Python Power: Why 2026 Belongs to Coders Who Think in Python
If the past decade was about learning to code, the next one is about coding smarter. And in 2026, the smartest move for any IT enthusiast is learning Python — the language that powers AI models, automates the web, and drives data decisions across ind

The Tableau Revolution of 2025
"In a world drowning in data, companies aren’t just looking for analysts—they’re hunting for storytellers who can turn numbers into decisions. Enter Tableau, the #1 data visualization tool used by 86% of Fortune 500 companies (Tableau, 2024). Whether
From Student to AI Pro: What Does Prompt Engineering Entail and How Do You Start?
Explore the growing field of prompt engineering, a vital skill for AI enthusiasts. Learn how to craft optimized prompts for tools like ChatGPT and Gemini, and discover the career opportunities and skills needed to succeed in this fast-evolving indust

How Security Classification Guides Strengthen Data Protection in Modern Cybersecurity
A Security Classification Guide (SCG) defines data protection standards, ensuring sensitive information is handled securely across all levels. By outlining confidentiality, access controls, and declassification procedures, SCGs strengthen cybersecuri

Artificial Intelligence – A Growing Field of Study for Modern Learners
Artificial Intelligence is becoming a top study choice due to high job demand and future scope. This blog explains key subjects, career opportunities, and a simple AI study roadmap to help beginners start learning and build a strong career in the AI

Java in 2026: Why This ‘Old’ Language Is Still Your Golden Ticket to a Tech Career (And Where to Learn It!
Think Java is old news? Think again! 90% of Fortune 500 companies (yes, including Google, Amazon, and Netflix) run on Java (Oracle, 2025). From Android apps to banking systems, Java is the backbone of tech—and Sulekha IT Services is your fast track t