Advancements in Cybersecurity technology to security 2.0

Among various emerging technologies, cybersecurity is an ever-proliferating career path for professionals and beginners. Moreover, cybersecurity is under immense pressure to move from signature-based detection methods to Behavioral Analytics.
In the old method or technique, security protection or hardening infrastructure security has failed to protect the data. On the other hand, having many layers to protect the organization even failed from security or data breaches.
As digital usage increases, zero vulnerabilities and social engineering are impossible, but it is significant contributors to these attacks. Cyberattacks are becoming more expensive as well. IBM revealed 2018 that the average cost of a cyberattack worldwide was USD 3,860,000. This price included costs for things like legal fees and clientele losses.
Anomaly-based Computer security systems
Cybersecurity tools have been updated and enable them to scan the traffic activity and ensure no malicious activities in the patterns.
This is a significant advantage for organizations moving from signature-based to anomaly-based detection.
For example, firewalls aid in finding or detecting malicious activities in the server and analyze whether servers accept multiple connections from new clients at a higher rate than average.
This would indicate that the connections were fraudulent and originated from a botnet. These connections would, therefore, be terminated. Many cybersecurity vendors developed tools that let organizations analyze real-time threats, thus thwarting attacks from unknown attack vectors.
On the other hand, Anomaly-based security tools have solved various security-related problems. Cybersecurity tools initially aid in finding malicious activities and provide threat reports to take necessary measures to protect the system or network.
These threat-analyzing tools could have been more efficient in securing or determining threats previously and providing active measures initially.
False positives were making the security tools unreliable. The introduction of anomaly-based security tools helps in analyzing real threats and how to stop cyber attacks.
Additionally, anomaly-based computer security systems made detection easier and more accessible. Initially, cybersecurity tools had to check with many signatures, which slowed network and system performance. On the other hand, Anomaly-based tools analyze real-time threats and evaluate whether traffic or apps have abnormal behavior.
Lastly, anomaly-based tools aid in encountering many social engineering attacks. These tools read packet headers to determine the origin and destination IP addresses, allowing traffic from known sources to pass through. Traffic from unknown sources was subjected to extensive checks to determine whether the origin had been blacklisted or reported as malicious by other security tools.
In conclusion, the advancements in cybersecurity technology have paved the way for Security 2.0, offering a range of innovative solutions that provide enhanced protection and peace of mind. These advancements have revolutionized the security landscape from biometric authentication to artificial intelligence-powered surveillance systems. With improved threat detection, faster response times, and increased efficiency, Security 2.0 is poised to address the evolving challenges of the digital age. As technology continues to evolve, we can expect further advancements in Security 2.0, ensuring a safer and more secure future for individuals, organizations, and society.
Find a course provider to learn Cyber Security
Java training | J2EE training | J2EE Jboss training | Apache JMeter trainingTake the next step towards your professional goals in Cyber Security
Don't hesitate to talk with our course advisor right now
Receive a call
Contact NowMake a call
+1-732-338-7323Take our FREE Skill Assessment Test to discover your strengths and earn a certificate upon completion.
Enroll for the next batch
hands on cyber security training
- Apr 15 2026
- Online
cyber security training courses
- Apr 16 2026
- Online
cyber security training courses
- Apr 17 2026
- Online
Related blogs on Cyber Security to learn more

How Security Classification Guides Strengthen Data Protection in Modern Cybersecurity
A Security Classification Guide (SCG) defines data protection standards, ensuring sensitive information is handled securely across all levels. By outlining confidentiality, access controls, and declassification procedures, SCGs strengthen cybersecuri
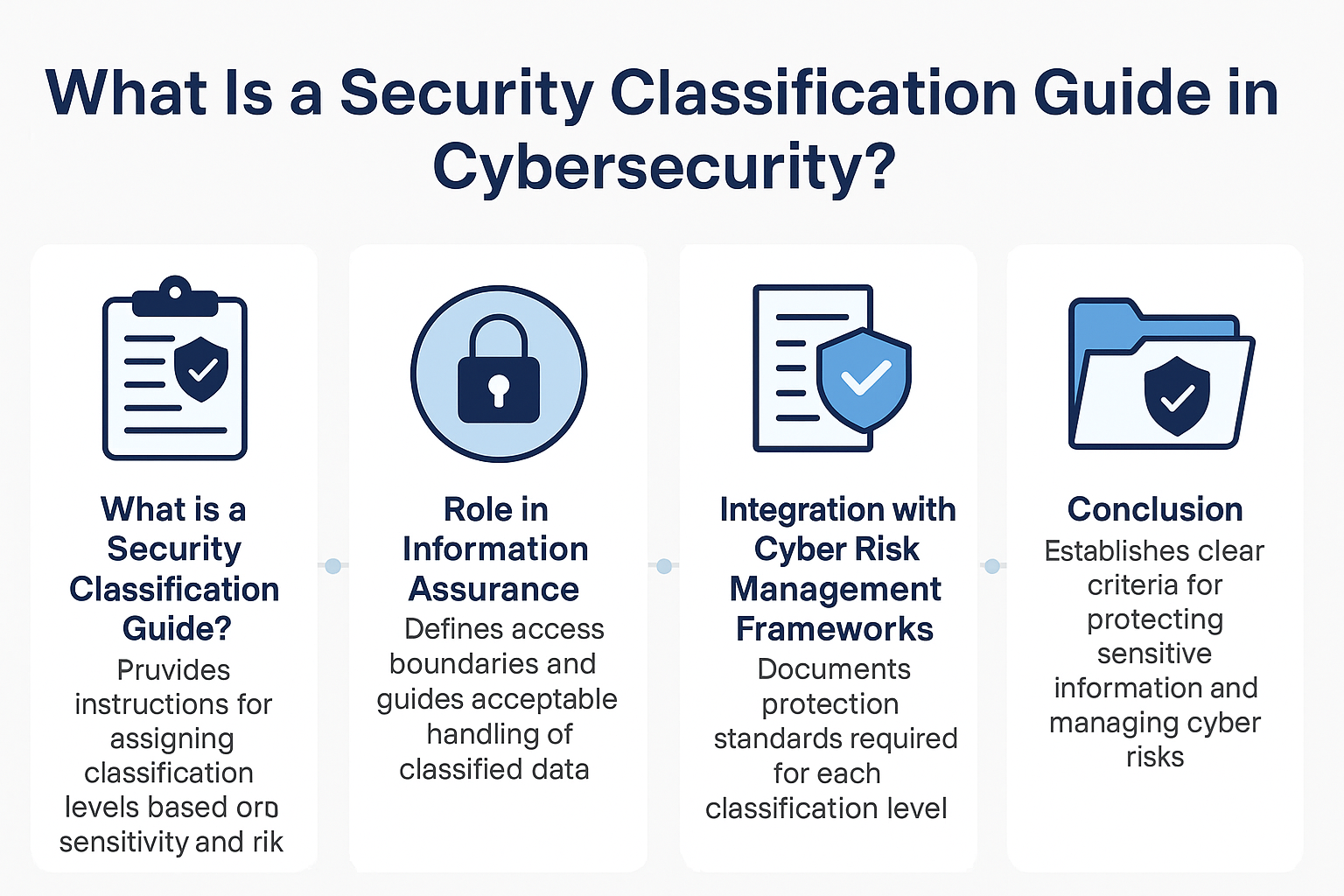
What Is a Security Classification Guide in Cybersecurity?
A Security Classification Guide (SCG) defines how to categorize information assets by sensitivity, with clear instructions from authorized officials to ensure consistent, compliant data handling.

Cybersecurity Training: Powering Digital Defense
Explore top cybersecurity training programs in the USA to meet rising demand in digital defense. Learn about certifications, salaries, and career opportunities in this high-growth field.

What Does a Cybersecurity Analyst Do? 2025
Discover the vital role of a Cybersecurity Analyst in 2025, protecting organizations from evolving cyber threats through monitoring, threat assessment, and incident response. Learn about career paths, key skills, certifications, and why now is the be
What essential skills and trends should cybersecurity professionals navigate in 2024?
Cybersecurity professionals in 2024 must master a diverse skillset, from cloud security and AI to soft skills like communication and problem-solving, to stay ahead of evolving cyber threats and regulations.

What Does a Cybersecurity Analyst Do?
Learn about the role of a Cybersecurity Analyst, responsible for protecting an organization's computer networks from cyberattacks.

10 Popular Cybersecurity Certifications
From CompTIA Security+ to CISSP, these certifications can boost your career and demonstrate your commitment to protecting computer systems and networks.

What are the most popular technical certifications for future career advancement?
Unlock your potential with insights into 5 popular technical certifications for future career growth, spanning cybersecurity, blockchain, cloud computing and more. Explore pathways for professional advancement today.

How to Become a Security Architect: 2024 Career Guide
How to Become a Security Architect: 2024 Career Guide In today's fast-paced and digitally interconnected world, the role of a Security Architect
Latest blogs on technology to explore

Drug Safety & Pharmacovigilance: Your 2026 Career Passport to a Booming Healthcare Industry!
Why This Course Is the Hottest Ticket for Science Grads & Healthcare Pros (No Lab Coat Required!)" The Exploding Demand for Drug Safety Experts "Did you know? The global pharmacovigilance market is set to hit $12.5B by 2026 (Grand View Research, 202

Launch Your Tech Career: Why Mastering AWS Foundation is Your Golden Ticket in 2026
There’s one skill that can open all those doors — Amazon Web Services (AWS) Foundation
Data Science in 2026: The Hottest Skill of the Decade (And How Sulekha IT Services Helps You Master It!)
Data Science: The Career that’s everywhere—and Nowhere Near Slowing Down "From Netflix recommendations to self-driving cars, data science is the secret sauce behind the tech you use every day. And here’s the kicker: The U.S. alone will have 11.5 mill

Salesforce Admin in 2026: The Career Goldmine You Didn’t Know You Needed (And How to Break In!)
The Salesforce Boom: Why Admins Are in Crazy Demand "Did you know? Salesforce is the 1 CRM platform worldwide, used by 150,000+ companies—including giants like Amazon, Coca-Cola, and Spotify (Salesforce, 2025). And here’s the kicker: Every single one

Python Power: Why 2026 Belongs to Coders Who Think in Python
If the past decade was about learning to code, the next one is about coding smarter. And in 2026, the smartest move for any IT enthusiast is learning Python — the language that powers AI models, automates the web, and drives data decisions across ind

The Tableau Revolution of 2025
"In a world drowning in data, companies aren’t just looking for analysts—they’re hunting for storytellers who can turn numbers into decisions. Enter Tableau, the #1 data visualization tool used by 86% of Fortune 500 companies (Tableau, 2024). Whether
From Student to AI Pro: What Does Prompt Engineering Entail and How Do You Start?
Explore the growing field of prompt engineering, a vital skill for AI enthusiasts. Learn how to craft optimized prompts for tools like ChatGPT and Gemini, and discover the career opportunities and skills needed to succeed in this fast-evolving indust

How Security Classification Guides Strengthen Data Protection in Modern Cybersecurity
A Security Classification Guide (SCG) defines data protection standards, ensuring sensitive information is handled securely across all levels. By outlining confidentiality, access controls, and declassification procedures, SCGs strengthen cybersecuri

Artificial Intelligence – A Growing Field of Study for Modern Learners
Artificial Intelligence is becoming a top study choice due to high job demand and future scope. This blog explains key subjects, career opportunities, and a simple AI study roadmap to help beginners start learning and build a strong career in the AI

Java in 2026: Why This ‘Old’ Language Is Still Your Golden Ticket to a Tech Career (And Where to Learn It!
Think Java is old news? Think again! 90% of Fortune 500 companies (yes, including Google, Amazon, and Netflix) run on Java (Oracle, 2025). From Android apps to banking systems, Java is the backbone of tech—and Sulekha IT Services is your fast track t
